On the Safe Side: Top Modules for Password Security in Drupal
Passwords are little gatekeepers that take care of securing a website’s user accounts. Considering their mission, they certainly need to be strong. Their strength can be especially crucial if a website contains sensitive information or if a particular user has a lot of permissions.
To equip your little security guards with shiny armor and make them unbreakable, you will need a decent password policy. The great news is that it is much easier to implement with the Drupal CMS. Drupal is highly rated for password security and offers plenty of great features in this sphere. We will discuss all this and more in today’s article, so let’s get started.
The keystones of a secure website password policy
A website password policy is a set of rules and measures for encouraging users to create strong passwords and for otherwise ensuring login security. It is often a part of the organization’s overall security policies.
The password policy can be advisory or it can be implemented programmatically via the website. The power of a website here cannot be underestimated. Your site can be your great security assistant that guides users through the process of creating passwords, imposes certain requirements, and automatically applies other login security features.
When deciding on the policy, you may find it very tempting to enforce super complicated password requirements in the name of security. However, this may lead to users having to save their passwords somewhere else, which introduces another security risk. And, of course, we also need to remember that cumbersome requirements may discourage registrations.

That said, shaping your password policy needs the right balance. The policy, and login security in general, should be based on the type of website you have and the level of data protection it really needs. Let’s say, e-commerce payments or online healthcare consultations need to be more secure than uploading a simple blog.
Your country’s government may also define the password policy that websites related to government services have to follow. For example, there is the United States Department of Commerce's National Institute of Standards and Technology (NIST) with its standards for password policy. It is a widely respected set of guidelines that are a good basis for any website, not just in the government sphere. The NIST guidelines are focused on usability, emphasizing that overly strict rules may have adverse effects. For example, it is not recommended to enforce regular password changes because in this case, users are likely to choose worse passwords. The exception is when a password has been compromised.
No matter how strict your password policy is, a very important thing to remember while implementing it is to make sure your website provides comprehensive feedback to users on every step of creating and using their passwords.
A guide to password security in Drupal
Let’s see why Drupal has a good reputation for password security. The Drupal core has a strong password management system that helps Drupal fulfill or exceed many of NIST’s recommendations. Here are some examples of the best Drupal core’s password security features.
- It’s convenient for users to see the strength of the password they are trying to create. NIST recommends this too. Luckily, Drupal features a password-strength meter that assists users in creating robust passwords. By default, Drupal advises users to make passwords 12 characters long (NIST recommends 8), use both lowercase and uppercase letters, numbers, and punctuation, as well as to make the password different from the username. This check is implemented in the form of suggestions, but additional contributed Drupal modules can help in imposing the requirements.
- The Drupal core limits unsuccessful authentication attempts to 5 per username every 6 hours. This allows real users to make mistakes but at the same time prevents brute-force attacks. Here, Drupal exceeds the NIST guidelines again because they recommend locking out accounts after 10 unsuccessful login attempts.
- Instead of just storing the passwords as they are, it is required to hash them. Hashing is a one-way transformation that turns a password into another string. Drupal does a really good job here by hashing passwords with the use of the SHA-512 algorithm. The CMS performs the hash function 65,500+ times instead of the recommended 10,000 times. What is more, Drupal only stores a salted hash value for each password. Salting means adding random data to hashing in order to increase the uniqueness of the strings and make them even harder to intercept.
In addition, there are plenty of contributed modules in Drupal to implement other password security features. Let’s take a look at some of them.
Top contributed Drupal modules for your secure password policy
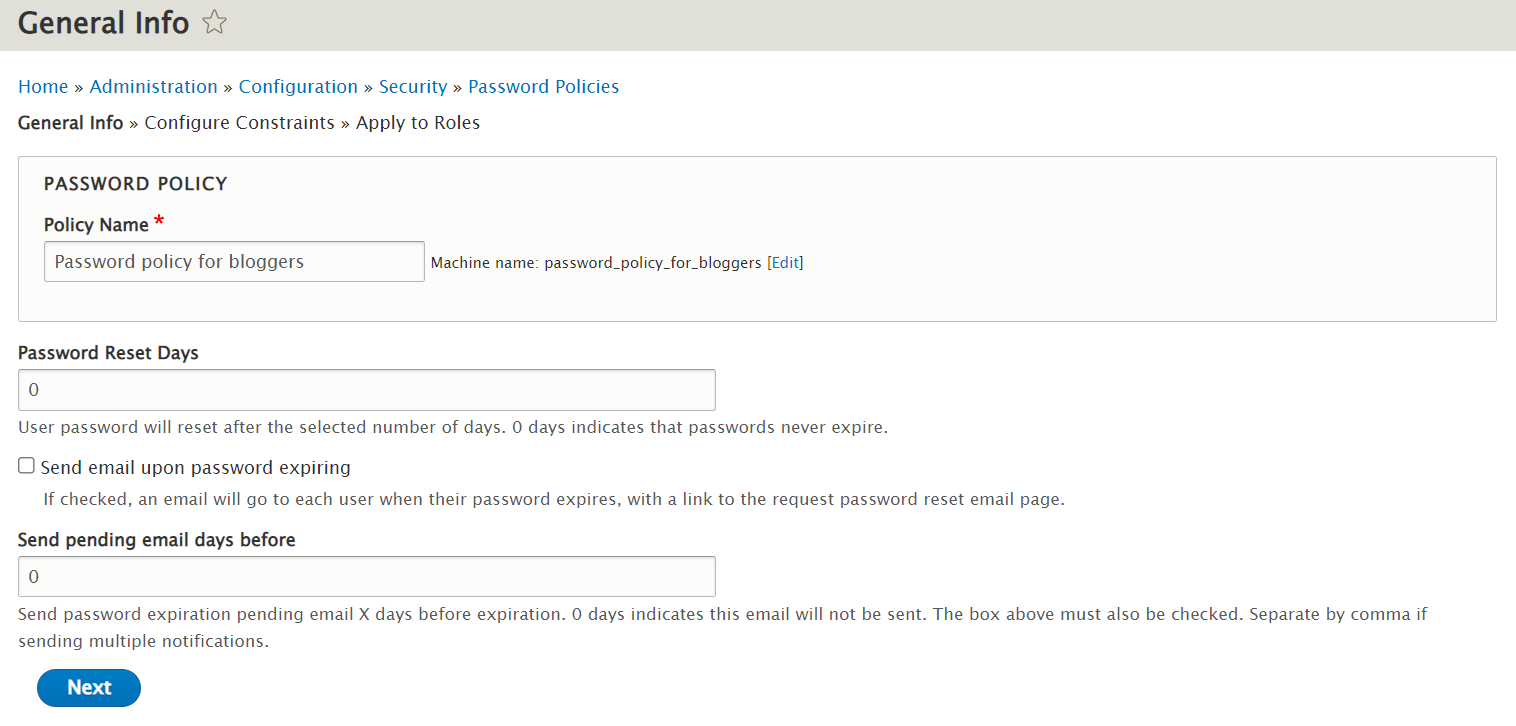
Password Policy
The Password Policy module provides an interface for you to shape specific password policies and apply them to different roles.
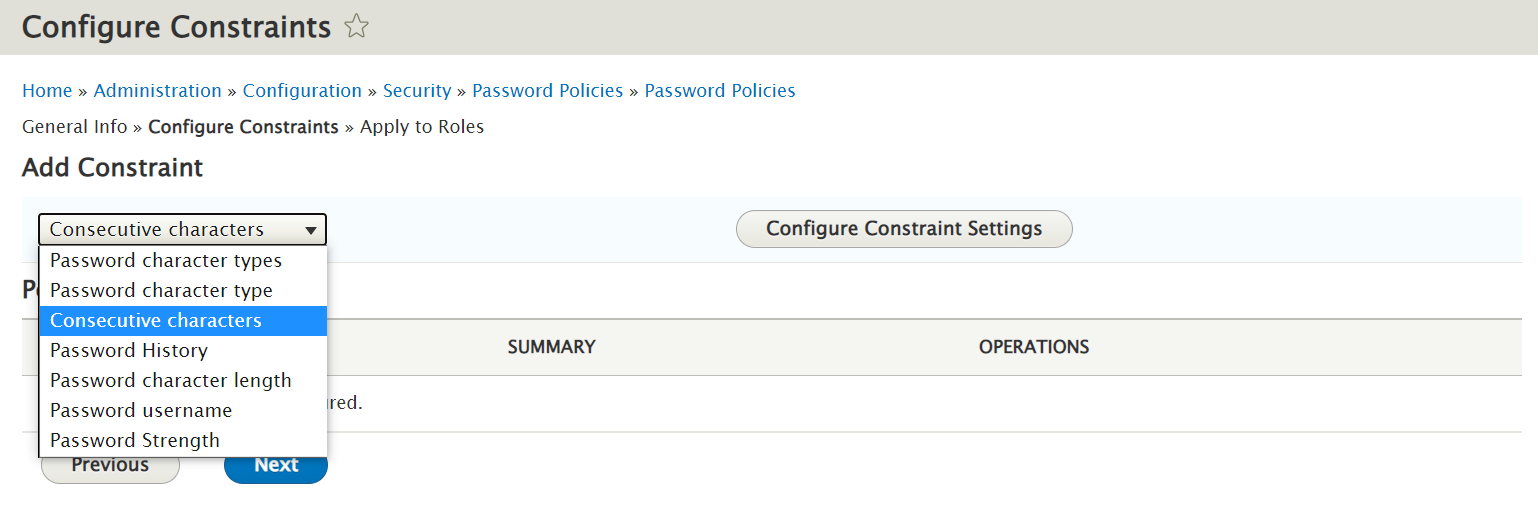
The policies are sets of configurable constraints that you may impose in order to make passwords stronger. For example, you can:
- Set the minimum number of different character types (uppercase letters, lowercase letters, numbers, and more)
- Set the minimum number of characters of a particular type (for example, if you set the uppercase constraint parameter to 2, users will need to create passwords containing two uppercase letters)
- Limit the number of consecutive characters
- Limit the repeated use of the same password (module will check the collection of previously used hashed passwords)
- Set the minimum character length
- Restrict the use of usernames in passwords
- Apply a special “Password strength” constraint that deals with the use of dictionary words, years, dates, and much more
The module also has a password expiration functionality with optional user account blocking once the password has expired. However, as mentioned above, this is not recommended by NIST, so administrators should be careful with this feature. In the module’s settings, choosing “0” means that passwords never expire.
Password Strength
We need to mention a popular module named Password Strength. Beginning with the Drupal 8 version, it works as a plugin for the above described Password Policy.
It performs password strength measurement and server-side enforcement. The module provides a system for administrators to define explicit requirements.
To measure the password strength, it detects the underlying patterns in them such as the use of common words, sequence of characters, dates, and more. The module sums up the strength of all the patterns detected in a password.
Better Passwords
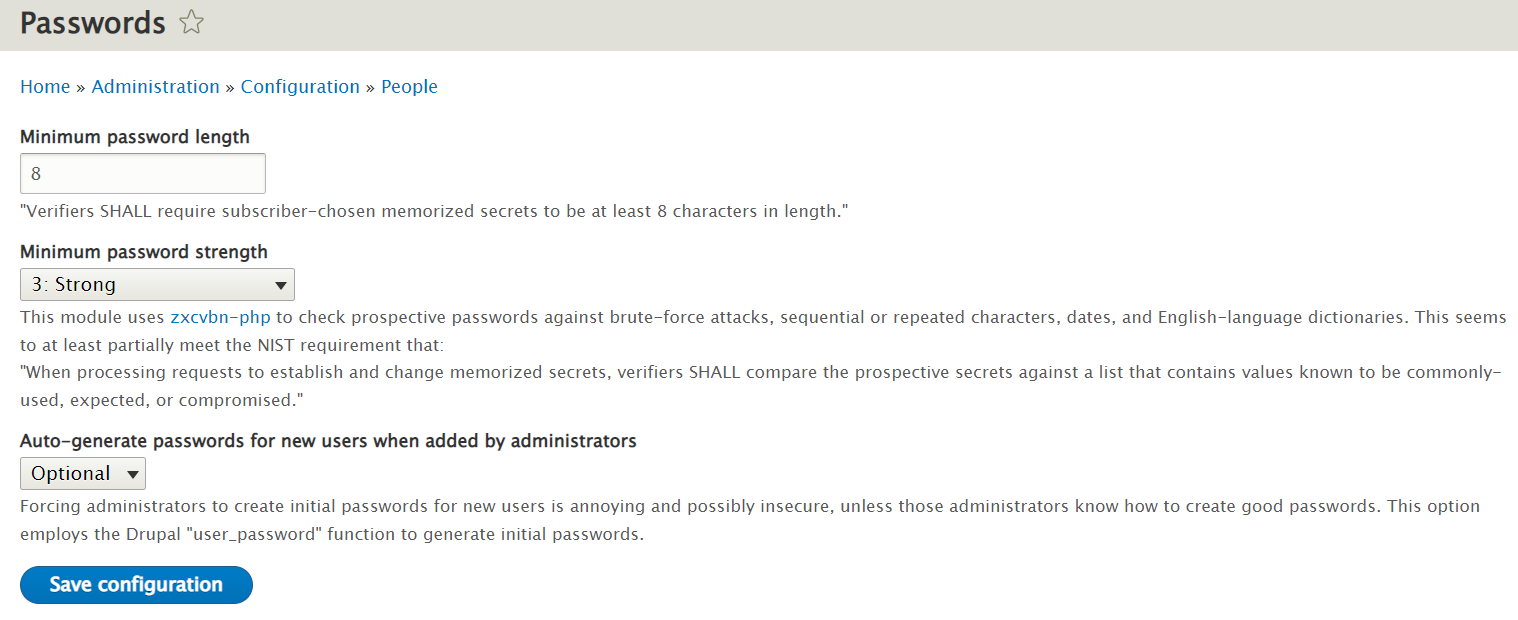
The creators of the Better Passwords module emphasize that their tool is aimed at fulfilling the NIST recommendations. In the module’s settings, you will be able to define:
- The minimum password length
The module’s developers remind us that NIST recommends a length of 8 characters.
- The level of password strength
The 5 levels are “don't check,” weak, moderate, strong, and strongest. The module uses the Zxcvbn-PHP library to check the strength of potential passwords against brute-force attacks. Among other things, it searches for sequential or repeated characters, dates, and dictionary words. While creating a password, a user gets an evaluation of its potential strength together with recommendations on how to make it more secure.
- Whether to allow the auto-generate feature for the passwords of new users when added by administrators
When this feature is used, the password is sent to the user. This is helpful because creating passwords can be annoying for administrators, not to mention the security aspect of a user creating a password for another user.
Two-factor Authentication (TFA)
It’s possible to add an extra layer of security to your Drupal website’s authentication process. Let’s say, you will be able to double-check who is knocking on your website’s door with the help of solutions like Time-based One Time Passwords (TOTP), SMS codes, or pre-generated codes. The Two-factor Authentication (TFA) module enables you to add them all.
This Drupal module easily integrates with any third-party services such as FreeOTP, Google Authenticator, Authy, and more. It provides handy interfaces in Drupal for working with them. The TFA module is very flexible thanks to its support for context-specific exceptions and fallback methods.
It should be mentioned that if an organization uses Single Sign-On (SSO) across systems, TFA or Multi-Factor Authentication (MFA) is preferably performed by the Identify Provider (IdP), and not an individual system or website. For example, organizations that use Active Directory for SSO should implement TFA on Active Directory so a user is fully authenticated before being passed back to the system they are wanting to access.
Since Drupal can be configured as an IdP for SSO to other systems, using TFA on Drupal is recommended in this scenario.
Secure Login
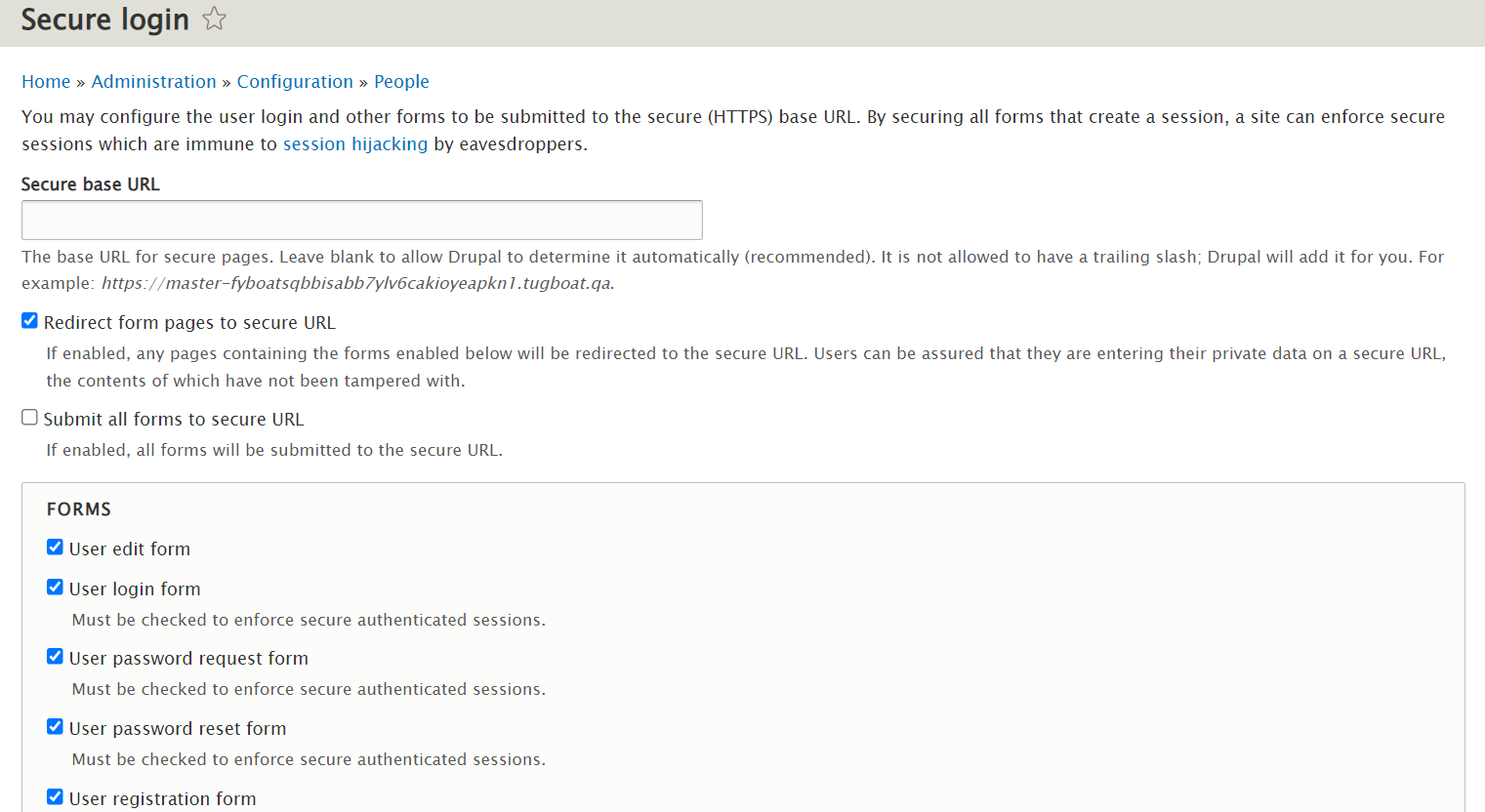
It is required to use encrypted connections in login forms, which means they should use the HTTPS (Hypertext Transfer Protocol Secure) protocol instead of HTTP. If a website is not configured for permanent HTTPS (and all websites should be), there is a useful Drupal module for websites that use both HTTP and HTTPS known as Secure Login.
The module helps you ensure all user login forms are submitted via HTTPS. This protects passwords and authenticated session cookies from the risk of being intercepted. In addition to the actual login forms, you can choose to include all kinds of forms in the protected list. An alternative to using this module is configuring the web server to redirect the pages to HTTPS.
Username Enumeration Prevention
Cybercriminals often use the username enumeration technique. It involves identifying valid usernames on a website and using them for further attacks. They make lists of user credentials (usernames and the corresponding passwords obtained through data breaches) to gain access to accounts through automated login requests.
The Username Enumeration Prevention module makes their malicious task significantly harder. It mitigates the common ways of identifying usernames on a website. To achieve this, the module warns administrators about an unsafe configuration and prevents the password reset form from showing whether a username exists on your Drupal website or not.
Login Security
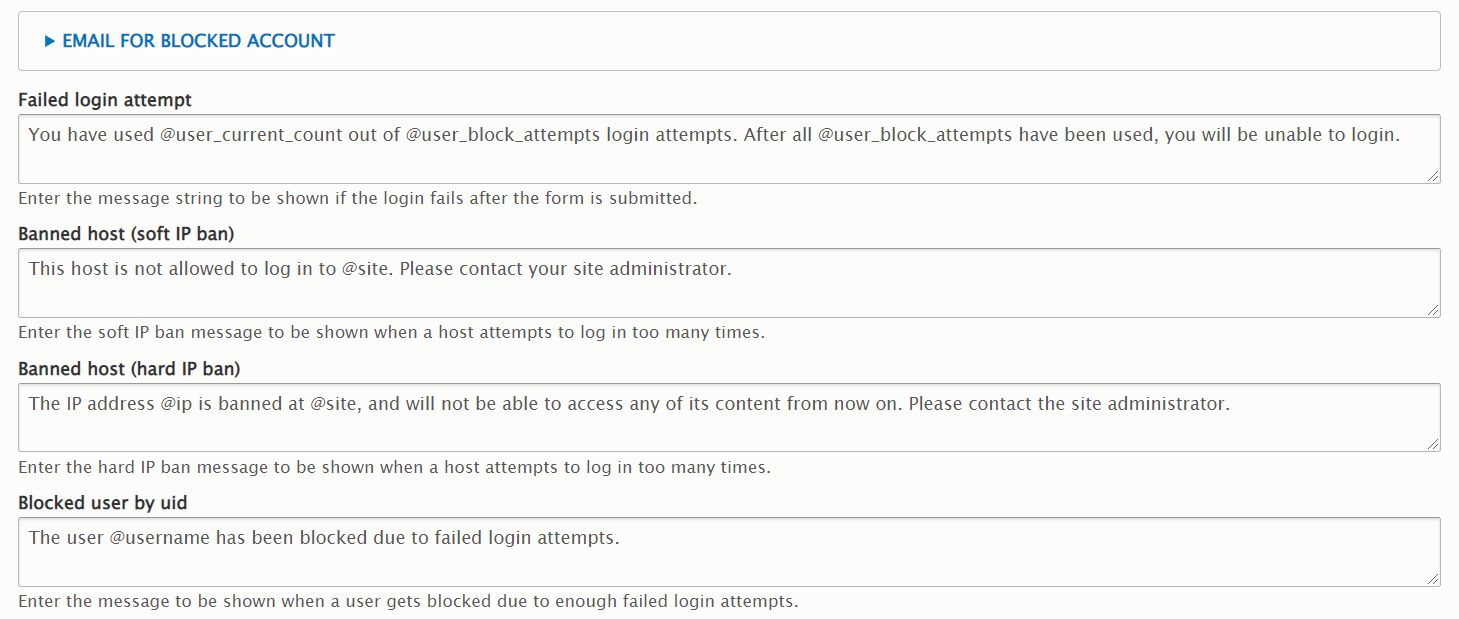
With the Login Security module, Drupal website administrators can add extra security features to the login forms. Namely, they can limit the number of invalid login attempts and block access by IP address on a temporary or permanent basis.
The module helps administrators stay aware of suspicious login behavior on their websites through notifications. They are informed about password and account guessing, brute-force attacks aimed at discovering the credentials, and other unwanted and dangerous actions. The module also offers a comprehensive system of configurable login-related notifications for users, as well as emails to the owners of the blocked or soon-to-be-blocked accounts.
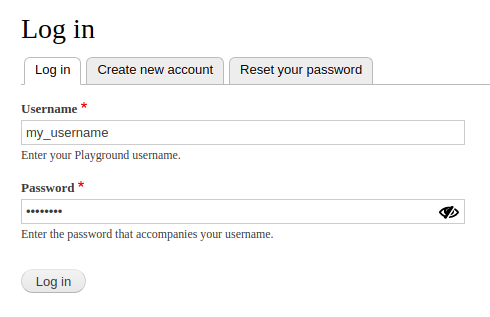
View Password
Enabling users to view their passwords before they hit “enter” is a good UX feature. This is also recommended by NIST as part of a good password policy. Drupal does not provide this out of the box, but the View Password module is here to help.
It is a lightweight module that adds a crossed-eye icon next to the password field on the login form. By toggling the icon, users switch between showing or hiding the password in the form. The module simply shows the entered password as plain text via JavaScript. It does not display any existing encrypted passwords from the database.
Restrict password change
There are scenarios where we want users to be able to add other users but not change their passwords for security reasons. The Restrict password change module comes in handy. It adds a “change other users’ password” permission.
When a user profile form is loaded, it checks for the proper permission and removes the password change option if the result is negative. The option of changing a user’s email address is removed as well.
Make sure your Drupal website is protected thanks to strong passwords in combination with other comprehensive security measures. You can always reach out to our team for professional security optimization or for creating a protected website from scratch on the super-safe Drupal CMS.